Free Cybersecurity Course
Enter the cybersecurity field with our free introductory course. Learn the basics and build a strong foundation.
A poisoned Florida-based water utility. A Channel 9 cyber attack that canceled morning shows on March 28 in Australia. A ransomware attack that shut down the largest US fuel pipeline and cost $5 million. These are only a few of the cyber incidents that have made news headlines in 2022—and the year is only halfway through.
The World Economic Forum rated cyber attacks as the fifth top risk of 2020, with a 0.05% detection rate in the US and estimated costs of $10.5 trillion by 2025. With 77% of security leaders anticipating critical infrastructure breaches, it is important for businesses, large and small, to be ready for future trends.
Did you know the most damaging cyber attacks are expected to cost businesses around $2 trillion by 2022? Learn how cyber attacks will affect businesses in 2022 in this guide.
What Are Cyber Attacks?
Cyber attacks are actions taken by cybercriminals that target computer systems, databases, infrastructures, and website visitors. According to the Internet Engineering Task Force, cyber-attacks constitute “an assault on system security that derives from an intelligent threat, i.e., an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of a system.”
The IT industry is expected to reach $170.4 billion in value by the end of 2022, which means the financial risk of cyber attacks is growing quickly.
6 Common Cyber Attacks and How To Prevent Them
Cyber attacks can happen at any time, and it’s important to distinguish between them in order to identify the root vulnerabilities and the right response. Attacks can be active or passive, and happen from within or outside of an organization. By recognizing attacks early, organizations can save money and prevent further access to confidential records by shutting down systems and notifying impacted stakeholders.
Below are some common types of cyber attacks, and how they work.
1. Phishing

Some 75% of organizations experienced phishing in 2020, with 96% of attacks coming by email. Phishing is an attack that uses emails and tricks people into downloading harmful messages. Many phishing attacks use legitimate links, a mix of valid and malicious code, incorrect URL shorteners and redirections, and altered brand logos to further the deception.
In 2020, companies reported COVID-related phishing emails, with more emails sent at low volumes to appear legitimate. Other cybercriminals used clickbait titles around the stimulus check, small business loans, and the presidential election to draw in unsuspecting readers.
Types of phishing include spear-phishing (which targets a company demographic, like system administrators), whaling (which focuses on the top-level executive), smishing (which employs text or SMS messages to attract attention), search engine phishing (which tries to push fake results to high visibility through SEO), email phishing, and vishing (which attacks via voicemail).
Prevention is one of the first solutions, which involves increasing security awareness and education. Other strategies include anti-phishing software and more robust email authentication.
After an organization detects phishing, they may need to change all user logins and wipe affected devices to continue operations.
Get To Know Other Cybersecurity Students
Gabrielle Oler
Systems Administrator at Coherent Technical Services
Dipen Patel
Cybersecurity Analyst at Accenture
Jose Mendoza
Cyber Security Career Track Student at Springboard
2. Ransomware

Ransomware is malware that inhibits users from accessing their software and demands financial compensation. Usually, ransomware spreads by spam or social engineering that causes malicious downloads.
In 2022, we expect to see more examples of encryption ransomware, which encrypts the victim’s files and then demands payment to restore operations (although this is proven to often fail, with 42% of organizations that paid criminals did not regain access to their files).
A recent poll by Kroll ranked ransomware as the most prevalent threat last year (~2,500 attacks reported by the Crime Complaint Center), with over one-third attributable to ransomware gangs. People working remotely became a new ransomware target during the pandemic, and ransom amounts involving cryptocurrency reached $50 million.
Once a company detects infection and reports ransomware to authorities, they can then work either pay the ransom, remove the malware or wipe all the data and try to restore with backups.
3. Malware

Malware stops devices from working or slows them down tremendously, using offensive agents like adware, spyware, viruses, worms, ransomware, or Trojans (when the attackers show themselves as useful to you in order to trick you). Malware can happen through an email attachment with malicious code or through file-sharing software that spreads harmful materials disguised as music or images.
There are many tools for addressing malware. Norton 361, Avast, Kaspersky, Bitdefender, Malware Bytes, and Webroot were ranked among the best software of 2022 to prevent malware. Firewalls and Intrusion Prevention Systems can also help secure data.
Researchers sometimes use a technique called sandboxing to isolate the code under investigation in a safe environment to detect malware.
4. Data Breach

Data breaches occur when confidential user information is exposed. Many companies reported data breaches in 2020, and this trend is expected to continue.
Last year, a hacker exposed 2.5 million account details at the alcohol delivery company Drizly. Prestige Software, the reservation system supporting Expedia, Booking.com, and Hotels.com, uncovered a leak of credit card numbers of more than 10 million customers dating back to 2013.
Most breaches are financially motivated (86%), but others are driven by espionage or human error. Once a data breach happens, companies need to take swift action to protect their image in the press and on social media and to avoid costly fines, which can range from $50,000 to $750,000+. Breaches usually surface through internal records, bank notifications, law enforcement officials, or customer reporting.
The first steps usually involve containing the breach by isolating affected systems, creating a communication strategy, delving into the details with a Personal Forensics Investigator, and bringing systems back online with enhanced security, such as regular monitoring of Intrusion Detection System and firewall logs.
5. Distributed Denial of Service Attack (DDoS)
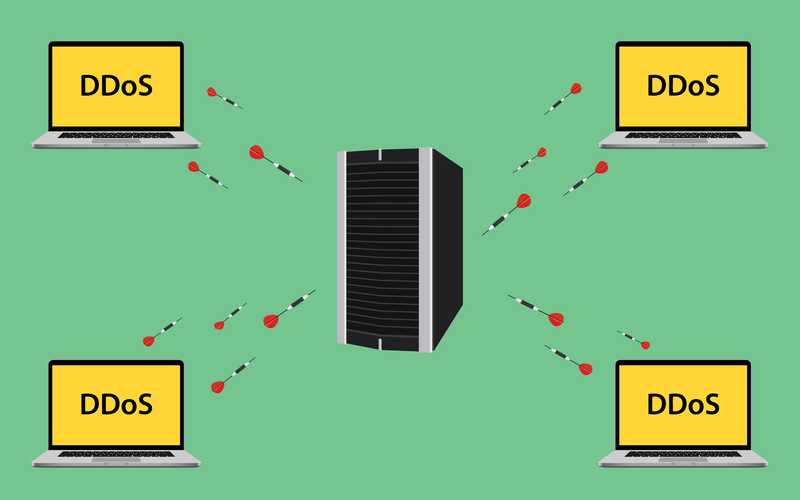
DDoS attacks happen when the intruder adds an unhealthy amount of traffic to a system or server, causing it to stop or pause operations. With IT downtime costing $300,000 to $1,000,000+ per hour, this can be very expensive. In 2020, Google revealed that it had been hit by a 2.5Tbps DoS attack, which was the largest attack to date, involving 180,000 web servers.
To protect against distributed denial of service attacks, it is important to make sure you use cloud-based web servers that can absorb traffic volume overflow, run regular security tests, update software and bandwidth, and work with Internet Service Providers or outsourced solutions to locate DoS mitigation services (here are some examples).
In the future, we need to be more prepared for burst (shorter) attacks and application-layer attacks and protect ourselves against exposed servers. One of the most common types of DDoS attacks is the smurf attack, which focuses on vulnerability within Internet Protocol (IP addresses) and Internet Control Message Protocol (ICMP).
6. Man in the Middle Attack (MitM)
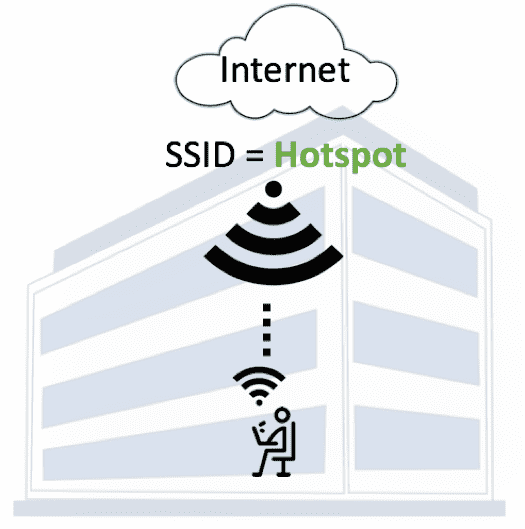
MitM attacks occur when an attacker intercepts and modifies electronic messages, sometimes to harm the relationship and spy on the conversation. An example is a fake wifi hotspot that mirrors the functionalities of the real one, deceiving users and changing air traffic flows. With the growing trend of remote work and digital communications, it is increasingly important for companies to use end-to-end encryption of messaging and video conferencing tools. In response to criticism early in the pandemic, Zoom rolled out end-to-end encryption to protect businesses during video calls.
Other types of attacks expected to continue in 2022 include SQL injection attacks (gaining unauthorized access to information via structured query language), zero-day exploits (quick exploitation of a security flaw), password attacks, session hijacking, brute force attacks (using a script to pull login credentials like usernames), and DNS tunneling.
Although these attacks cause reputational harm, financial damage, and the release of sensitive information, the growth in cyber-attacks means that the demand for cybersecurity and cybersecurity professionals, like cybersecurity analysts, will only go up in the coming year.
Since you’re here…
Interested in a career in cybersecurity? With or Cybersecurity Bootcamp, you’ll get a job in the industry, or we’ll return your tuition money. Test your skills with our free cybersecurity course, and check out our student reviews. We’re a safe bet. 🔒😉





![How To Become a Freelance Cybersecurity Expert [2023 Guide]](https://www.springboard.com/blog/wp-content/uploads/2023/10/how-to-become-a-freelance-cybersecurity-expert-2023-guide-380x235.jpeg)
