Free Cybersecurity Course
Enter the cybersecurity field with our free introductory course. Learn the basics and build a strong foundation.
With financial and health records having gone almost entirely digital, it’s easy to see why the field of cybersecurity has emerged as one of the most in-demand tech professionals. Cybersecurity professionals protect consumers’ personal information, safeguard against cyberattacks, and promote safer web browsing habits so organizations and private citizens can protect themselves from identity theft and other attacks.
Most people understand that cybersecurity professionals protect our information from hackers. But how they actually do that is less widely understood.
That’s why we’ve created this guide. Below, we’ll detail everything you need to know about cybersecurity so that you can better understand how this industry is shaping tomorrow’s world.
What Is Cybersecurity?
Cybersecurity is the practice of protecting systems, networks, and programs from cyberattacks and unauthorized access. Cyberattackers aim to destroy, alter, or access sensitive information for financial gain or to disrupt regular business operations. A cybersecurity strategy uses people, processes, and technology to safeguard an organization’s intellectual property and other important digital assets.
Why Does Cybersecurity Matter?
Cyberattacks cost organizations millions of dollars each year and lead to reputational damage. Organizations experience an average of 130 cyberattacks each year. In 2021, the global cost of cybercrime exceeded $6 trillion, and the problem is getting worse. According to Accenture, the average annual number of security breaches grew by 27.4% in 2020.
Data breaches also pose grave consequences for the average person. Cybercriminals use stolen personal information, such as a social security number, to impersonate someone, usually with the end goal of seizing their financial assets. Attackers also mount phishing attacks on personal computers and mobile devices to infect the device with malware—software designed to disrupt, damage, or gain unauthorized access to a system.
Companies need cybersecurity professionals for several reasons. These professionals play critical roles in protecting sensitive information, defending against cyber threats, and maintaining the security and integrity of computer systems and networks.
Their jobs include:
Protecting sensitive information
Cybersecurity professionals are responsible for safeguarding sensitive data, such as personally identifiable information (PII) or proprietary business data. They implement security controls, such as encryption, access controls, and identity and access management systems, to prevent unauthorized access and data breaches.
Defending against cyber threats
With the rise of advanced persistent threats and evolving cyber attacks, companies require cybersecurity professionals who are equipped with knowledge and expertise to identify and mitigate these threats. They are trained to detect and respond to various types of cyber threats, including phishing attacks, malware attacks, ransomware attacks, and supply chain attacks.
Maintaining the security of critical infrastructure
Critical infrastructure security is a vital aspect of cybersecurity. Cybersecurity professionals are involved in securing and protecting critical systems, such as power grids, transportation systems, and healthcare facilities, from potential cyber attacks that could disrupt essential services and jeopardize public safety.
Ensuring business continuity
Cybersecurity professionals help organizations establish business continuity plans and develop risk assessment frameworks to ensure that normal business processes can continue even in the face of cyber threats or attacks. They analyze security risks, implement security controls, and provide guidance to maintain the continuity of operations.
Enhancing network security
Cybersecurity professionals focus on maintaining the security of computer networks. They deploy perimeter security measures, such as firewalls and intrusion detection systems, to monitor and prevent unauthorized access. They also employ threat intelligence tools and technologies to stay updated on known and unknown threats, enabling proactive defense.
Collaborating with security analysts
Cybersecurity professionals work closely with security analysts to investigate security incidents, perform risk assessments, and develop security architectures. They collaborate to design and implement effective security controls and monitor the overall cybersecurity posture of the organization.
Adhering to regulatory compliance
Many industries have specific regulations and compliance requirements related to data security and privacy. Cybersecurity professionals ensure that organizations meet these regulatory obligations, such as those defined by the National Institute of Standards and Technology (NIST) or industry-specific regulations like HIPAA or GDPR.
Addressing insider threats
Insider threats, such as malicious employees or contractors, pose a significant risk to organizations. Cybersecurity professionals implement security measures and access controls to detect and mitigate insider threats, preventing unauthorized activities and data breaches from within the organization.
Evaluating and implementing cybersecurity solutions
As cybersecurity challenges continue to evolve, professionals in this field stay updated on emerging technologies and solutions. They assess and deploy key cybersecurity technologies, including antivirus software, advanced threat detection systems, cloud security solutions, and more, to enhance overall security measures.
Three Pillars of Cybersecurity: The Foundation of Effective Cybersecurity
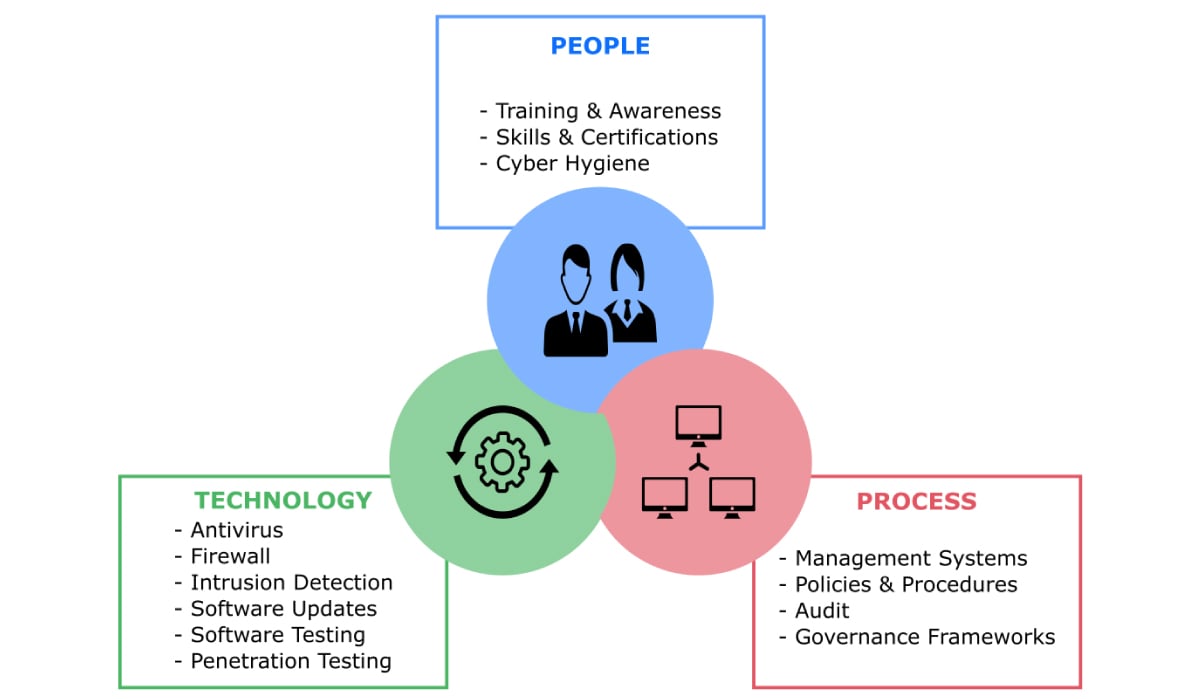
Cybersecurity is a framework that requires the marshaling of resources in a coordinated manner. Let’s break down what that looks like:
People
Organizations hire trained cybersecurity professionals to design and implement cybersecurity frameworks. They must also train their employees to recognize phishing scams and social engineering. People are almost always the weakest link in an organization’s cyber resiliency.
Processes
Processes and policies provide the frameworks for cybersecurity governance. These processes range from preventative strategies to avoid cyberattacks to real-time interventions in the event of cybercrime to identify and eliminate an intruder.
Technology
Technology refers to the IT infrastructure (hardware and software) organizations use to achieve cybersecurity. Examples include antivirus software and defensive AI that scans computer networks for anomalous behaviors and learns from prior cyberattacks. Cloud encryption technology secures data stored in the cloud by turning the information into unreadable code before it is stored.
CIA Triad: The Three Primary Objectives of Cybersecurity
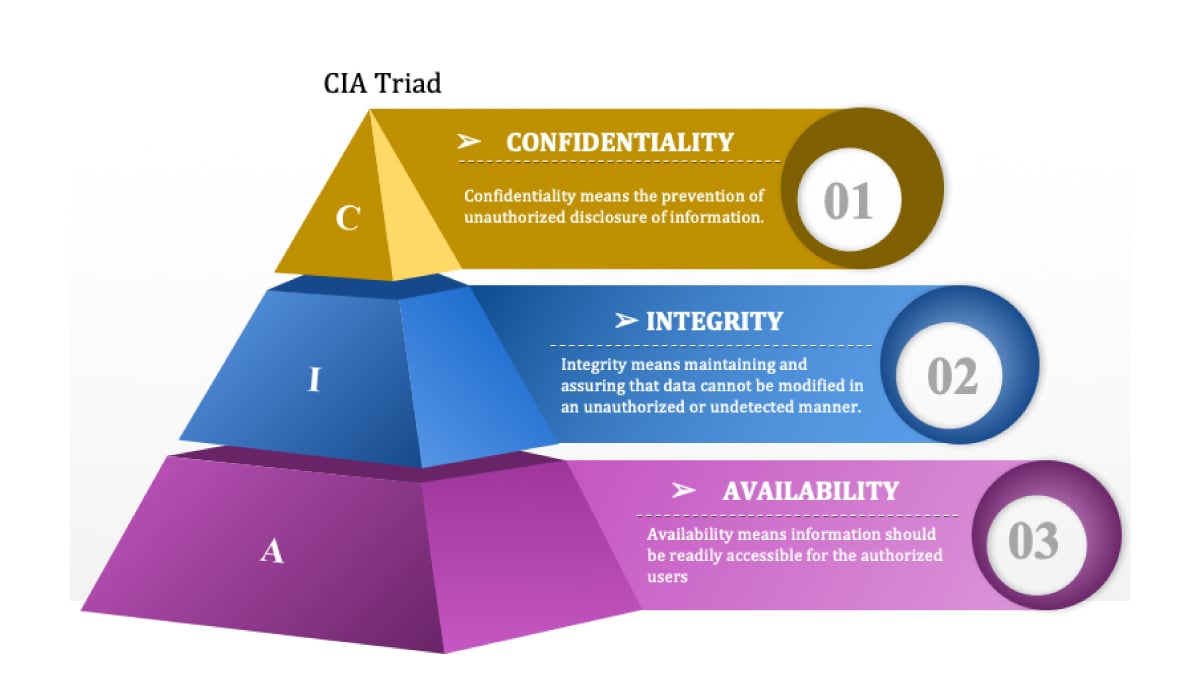
The CIA triad is a common model that explains the main objectives of any cybersecurity framework. This model helps security teams ensure all bases are covered using security best practices.
Confidentiality
Organizations must protect proprietary information and their consumer’s personal data. Access must be restricted to authorized users, and robust authentication protocols and user permission controls are needed to keep intruders out. For example, employees in unrelated departments should not have access to certain data because it could be liable to exploitation.
Integrity
Data must be accurate, trustworthy, and free from tampering. Data integrity can be maintained with access control and encryption. In some cases, data may be protected physically from outside sources that might corrupt it (particularly for businesses that use on-premise servers rather than cloud storage).
Availability
Ensuring systems, applications, and networks are functioning normally and haven’t been shut down by attackers. Data should be available to authorized users whenever they require it.
The Cybersecurity Process (NIST Cybersecurity Framework)
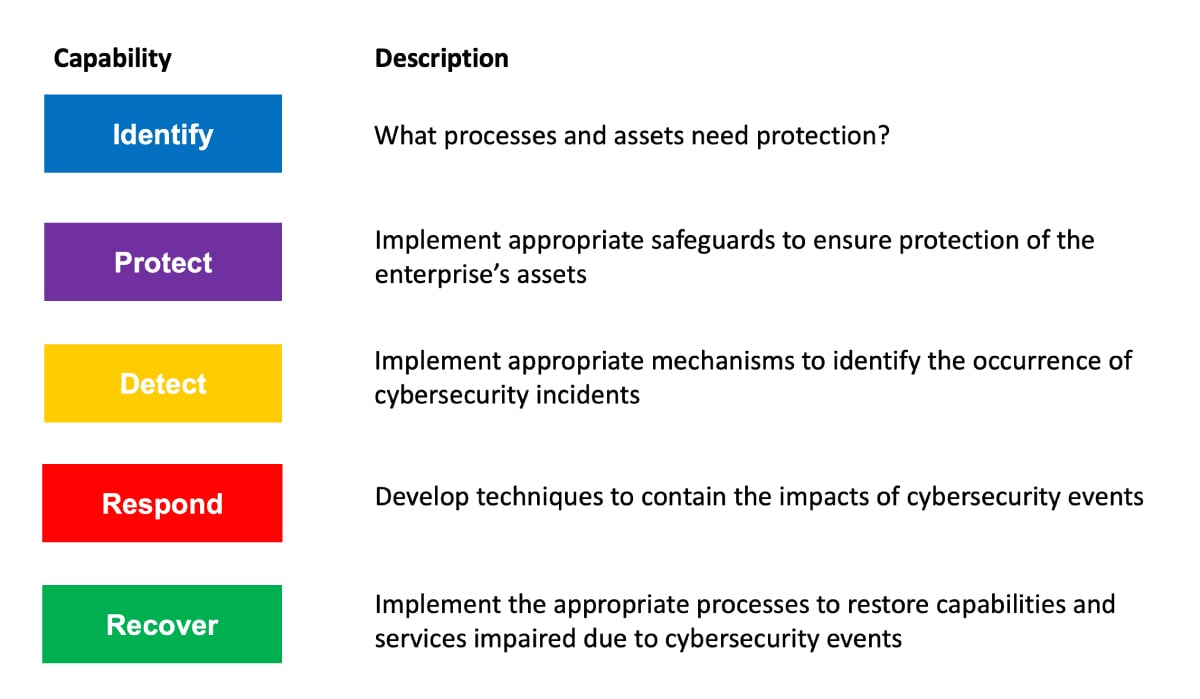
The NIST framework consists of standards, guidelines, and best practices to mitigate cybersecurity risk. The framework comes from the National Institute of Standards and Technology, a government agency formed by the U.S. Department of Commerce that develops cybersecurity standards for businesses, federal agencies, and the broader public. Here’s what that looks like in practice:
Identify
Determine the nature of the threat and identify the assets that need protection.
Protect
Implement appropriate security controls to protect the compromised asset and restore system function.
Detect
Determine the nature and impact of the threat. Implement continuous monitoring capabilities to track security events and see if protective measures are working.
Respond
Develop techniques to oust the intruder and limit the impact of the threat (threat containment).
Recover
This is the process of restoring any systems and services that were impaired during the attack and implementing improvements based on lessons learned.
Cybersecurity Types
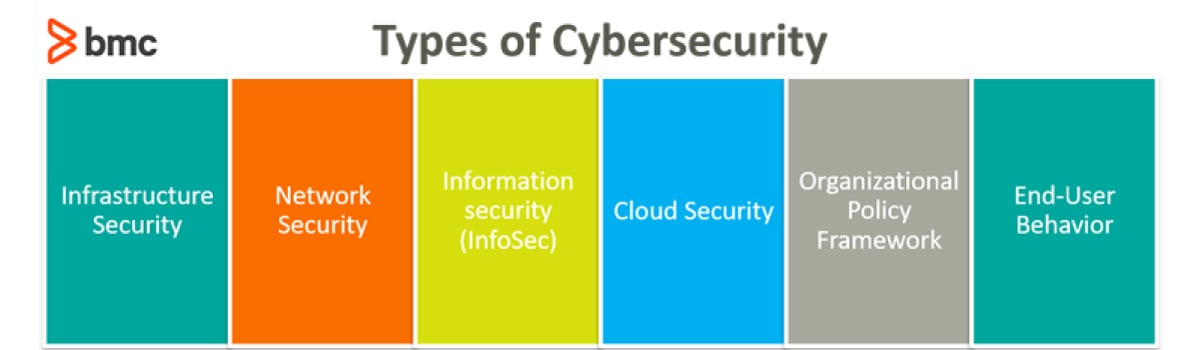
Cybersecurity can be categorized into five distinct strategies. Organizations often need a combination of approaches to secure themselves.
Network Security
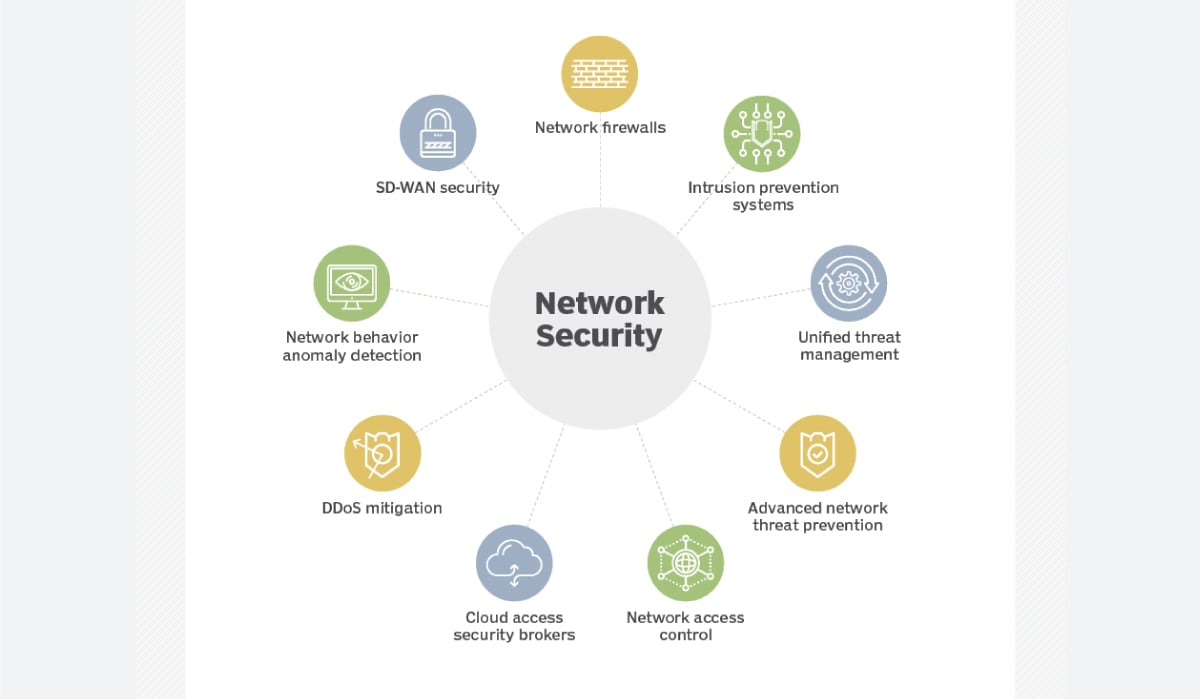
Network security is about protecting an organization’s computer networks from intrusion using data and access controls. Examples include Data Loss Prevention (DLP), IAM (Identity Access Management), NAC (Network Access Control), and NGFW (Next-Generation Firewall) application controls to enforce safe web use policies.
Get To Know Other Cybersecurity Students
Eric Rivera
IAM Security Specialist at Dearborn Group
Rafael Ayala
Mergers And Acquisitions at Autodesk
Catherine McKoy
Consumer Compliance Systems Analyst at Alaska USA Credit Union
Application Security
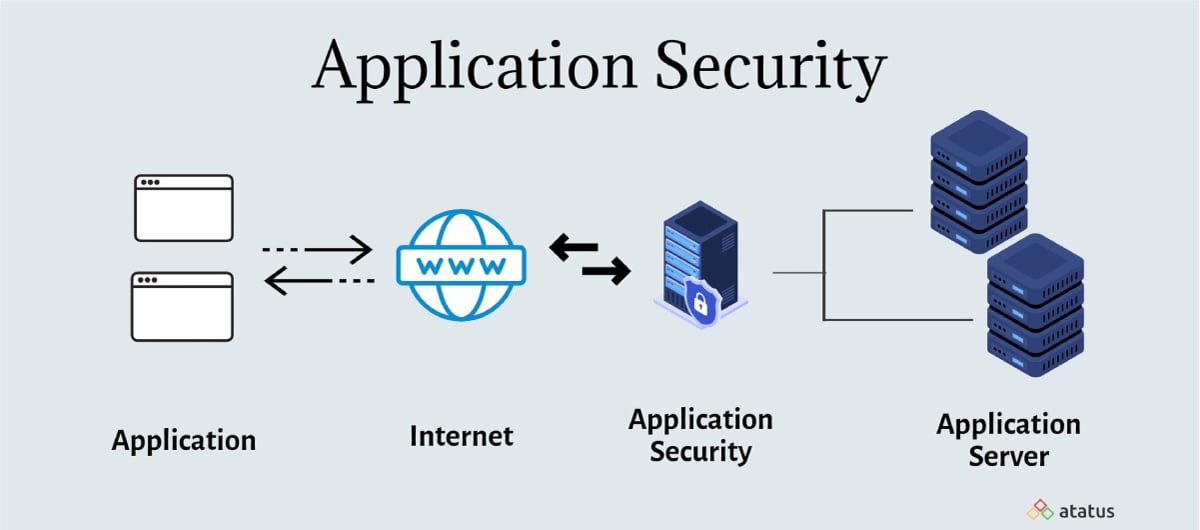
Application security offers protection for web applications to prevent data or code from being stolen or manipulated. These safeguards are implemented during the software development process but involve patches, upgrades, and other approaches to protect apps after deployment.
Cloud Security

Cloud security is the process of protecting data stored in the cloud from unauthorized access. While cloud computing providers manage the infrastructure, organizations that use their services must take extra precautions to secure their data.
Infrastructure Security
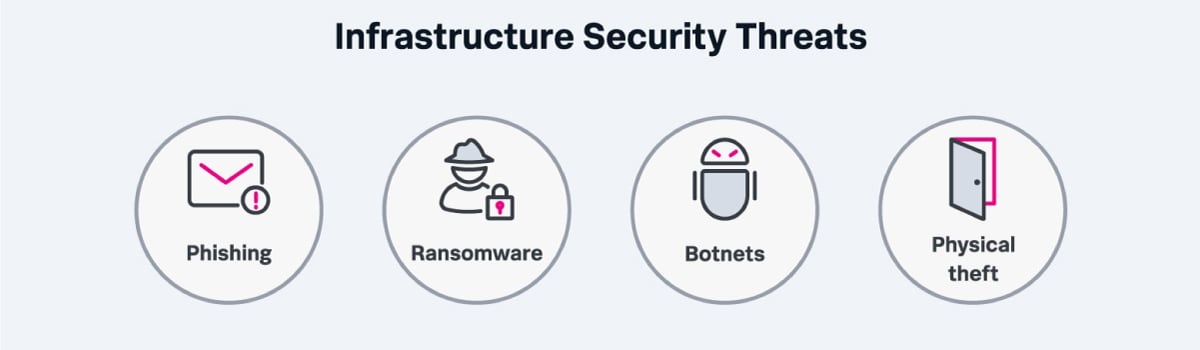
Infrastructure security is the process of safeguarding critical systems and assets from cyber threats. This typically includes hardware and software assets such as end-user devices, data center resources, networking systems, and cloud services. Organizations must also protect their assets from physical threats such as natural disasters, utility outages, theft, or vandalism.
Mobile Security

This is the process of employing user authentication and authorization across mobile devices, which is especially important as companies increasingly allow remote workers to use home Wifi networks.
Internet of Things (IoT) Security
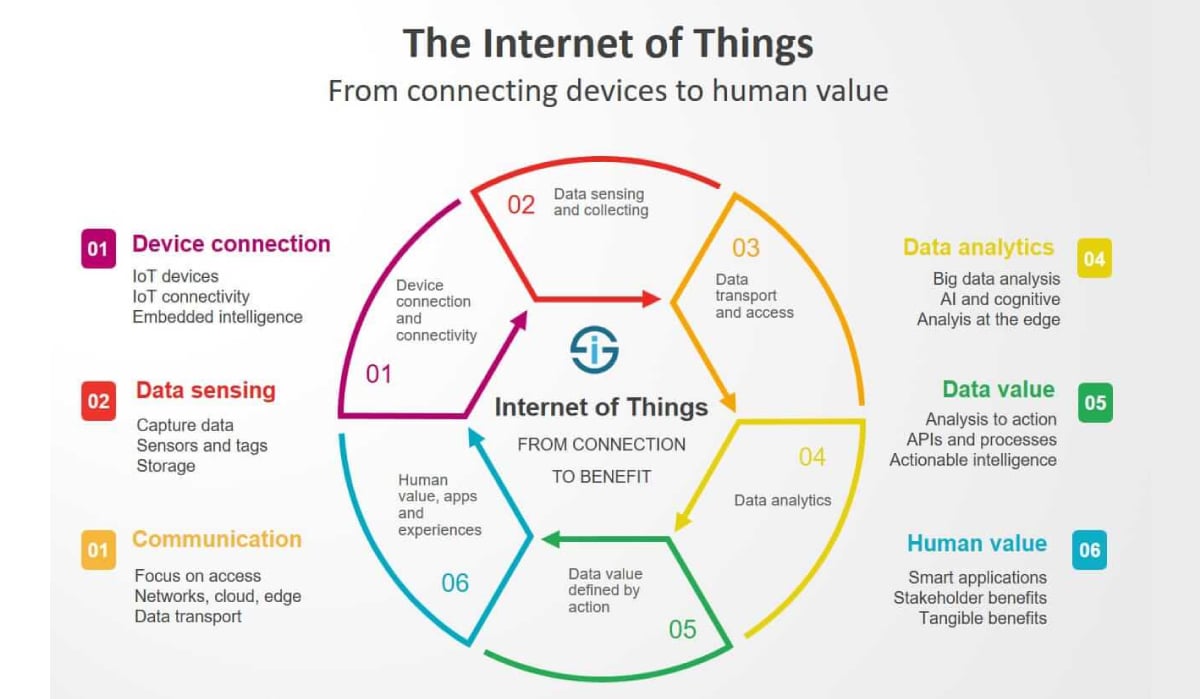
IoT-enabled devices, such as smart speakers, can be hacked and used to spy on people, as allowing devices to connect to the internet creates an additional attack surface for cybercriminals to exploit. IoT security seeks to end this.
Main Cyber Threats
Cybercriminals are continuously changing their strategies and uncovering new attack vectors. Here are some of the most common cyber threats you’ll see.
Malware
Malware is any malicious software designed to infiltrate computer networks to steal data or cause damage. Some examples include viruses, worms, spyware, adware, and ransomware.
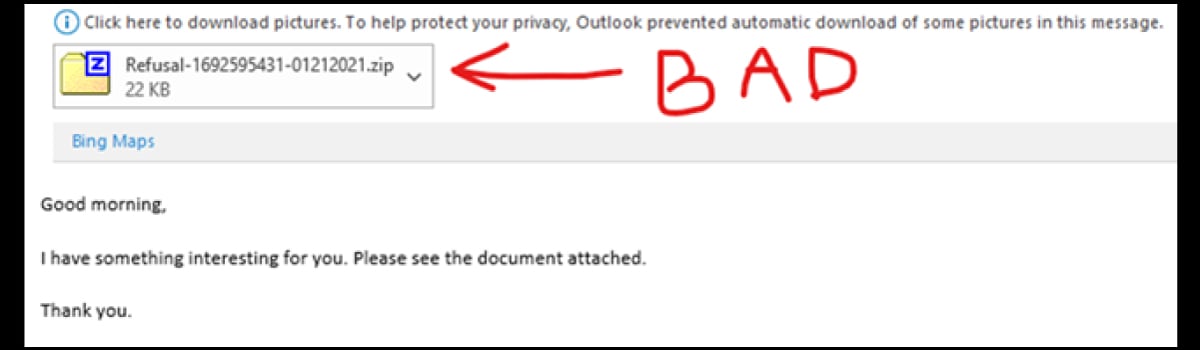
Phishing

Phishing is the process of sending fraudulent communications, purported to come from a trusted source, but is in fact embedded with malware. Phishing emails typically contain links to a spoofed website (a fake website made to look like the original) or a malicious attachment to persuade the victim to divulge their personal information.
Distributed Denial-of-Service (DDoS) Attack
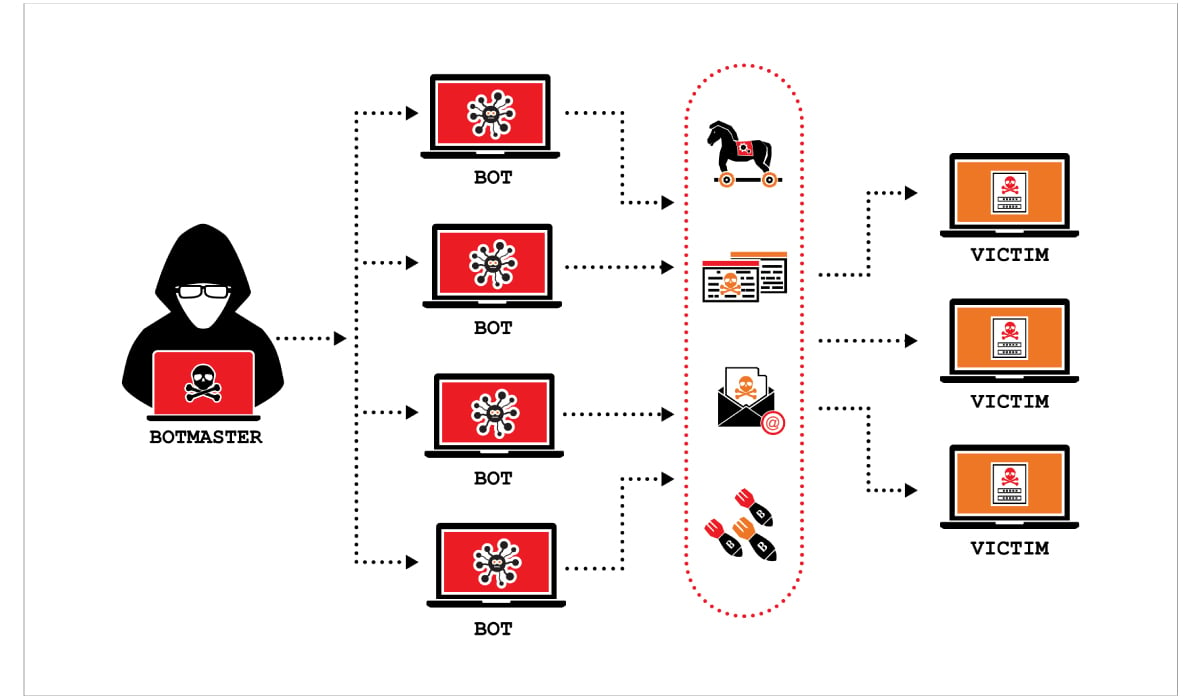
A DoS attack occurs when hackers flood a server with internet traffic to prevent legitimate users from accessing a website or application. DDoS uses a network of “zombie” computers coordinated by multiple botnet machines that instruct infected competitors to flood a website with fake requests.
Data Breaches
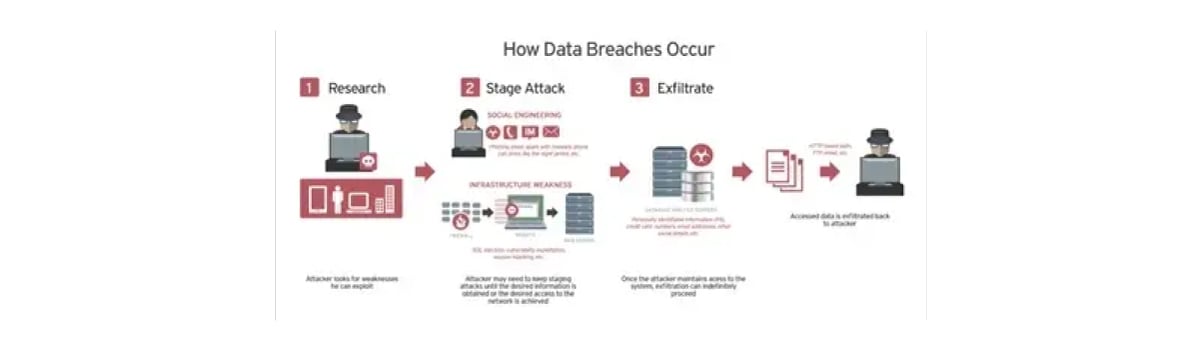
Hackers often attempt to gain access to a company’s servers or cloud storage to steal sensitive or confidential information. This is called a data breach.
SQL Injection
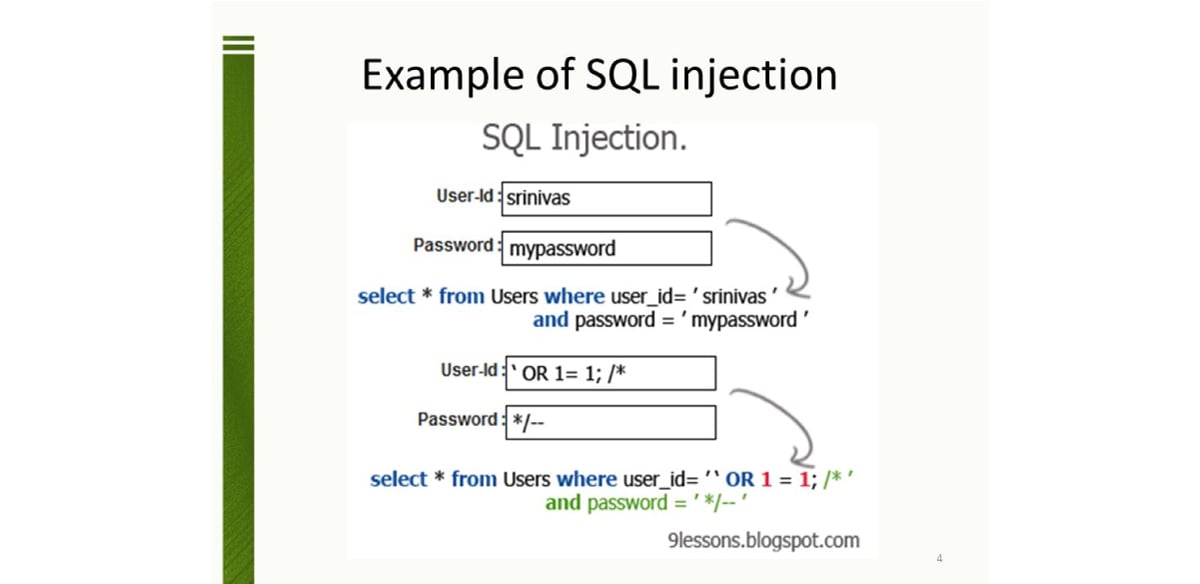
A code injection technique that can destroy a database. It allows an attacker to interfere with the queries an application makes to its database by inserting malicious SQL statements into an entry field for execution (i.e. instructing the database to dump the database contents to the attacker).
Ransomware
Ransomware is any type of malware that restricts access to a computer system, locks authorized users out of the system, or severely hampers system performance. Attackers will demand a ransom in exchange for the restoration of access.
Understanding the Cybersecurity Specialist
Cybersecurity specialists perform a range of tasks, from risk assessments to incident response. Security professionals may have expertise in a particular vendor’s product or experience in specific domains such as mobile applications. Let’s break down what that looks like.
What Does a Cybersecurity Specialist Do?
Cybersecurity specialists secure information systems by monitoring, detecting, investigating, and responding to security events. Here’s how they do that:
Identify and Assess Cybersecurity Risks
Security specialists anticipate future threats and advise companies on how to implement security controls to prevent breaches.
Develop and Implement Security Policies and Measures To Mitigate Risks
Cybersecurity specialists also implement policies to protect against threats such as viruses, worms, spyware, and other malware. They also develop and implement security measures to prevent data breaches and unauthorized access to systems.
Conduct Cybersecurity Audits
A cybersecurity audit is a comprehensive review of an organization’s IT infrastructure to identify security issues that may lead to a data breach. The audit determines the security of an organization’s data, operations, networks, systems, and physical security.
Respond to Cybersecurity Incidents
Most organizations have an incident response plan that outlines steps and procedures in the event of a data breach. The first step is to identify the threat and determine its severity. The next phase is to contain and eradicate the threat before it can cause further damage. Finally, post-incident recovery consists of reviewing lessons learned and adjusting security controls accordingly.
Maintain Up-to-Date Knowledge of Cybersecurity Threats and Trends
Cybercriminals are constantly adopting new strategies to breach security systems. So cybersecurity professionals must stay up to date on new attack vectors, advisories from vendors and government agencies, and recent accounts of high-impact security incidents.
Related Read: 10 Cybersecurity Trends You Should Be Familiar With
Monitor Potential Data Breaches and Investigate if Needed
Security professionals monitor network activity for signs of intrusion and investigate incidents when they occur. In the event of an attack, they perform a forensic analysis to reconstruct the events of a data breach and identify the source of the threat and determine if the intruder is still present.
Cybersecurity Tools

Now that we know what a cybersecurity professional does, let’s take a look at the tools they use to make that happen:

Source: Spiceworks
Intrusion Detection and Prevention
Intrusion Detection and Prevention Systems (IDPS & IPS) monitor network and IT environment activity 24/7 to detect malicious activity in real-time and block them either through an automated response or by alerting a security professional.
Packet Sniffers
A packet sniffer is a sniffer program that reads packets of data transmitted over the internet to monitor and validate network traffic. By monitoring internet traffic in real-time, data can be examined to diagnose any performance problems with servers, networks, hubs, and applications that might indicate interference.
Firewall
A firewall is a network security device that monitors traffic to and from a network. The system decides whether to allow or block traffic depending on a predetermined set of security rules. Firewalls are the first line of defense for most organizations.
Penetration Testing
Penetration testing is a type of ethical hacking where a licensed professional attempts to infiltrate a computer network with the organization’s permission to test its security posture. Any identified vulnerabilities are then patched to prevent a real attack.
Cryptography
Cryptography involves the process of encrypting information (changing data from readable plaintext to ciphertext) stored in the cloud or on a server so that it is indecipherable except to authorized users who possess a specific decryption key.
Virus and Malware Protection
Antivirus software scans computer systems for the presence of viruses and malware. Most antivirus software runs in the background once installed. Some software systems also provide customizable firewalls and website blocking.
Access Control
Managing user authentication and access is a key part of cybersecurity, as it ensures that authorized users have rapid access to a system or database while keeping intruders out. This includes policies for verifying user credentials, locking out suspected intruders, and creating passwords.
Endpoint Security
Endpoint security is the process of securing end-user devices such as computers, laptops, and mobile devices from being exploited by malicious actors. These security measures have become increasingly important as remote employees use home Wifi networks and privately owned devices, which are typically less secure than corporate networks.
Cybersecurity Career Opportunities
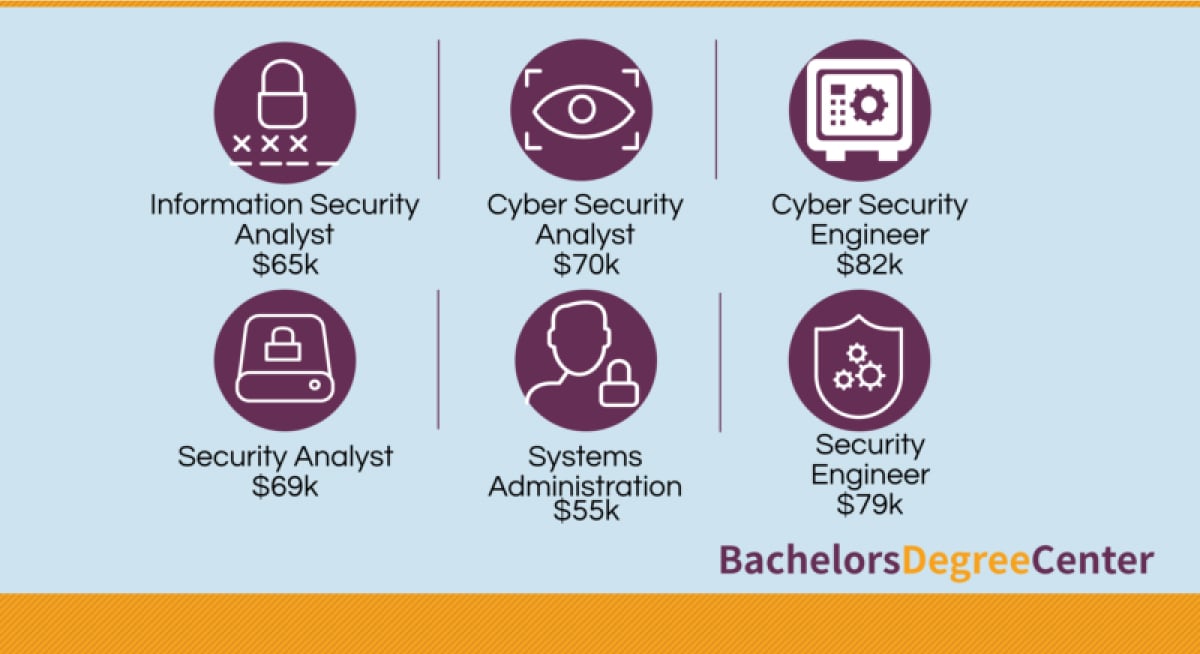
A study by Burning Glass showed that cybersecurity job postings grew by 94% between 2013-2019, and now account for 13% of all IT jobs. With cybercrime growing increasingly prevalent, organizations are investing heavily in cybersecurity controls. Here are some of the most common cybersecurity career opportunities:
Information Security Analyst
- What They Do
Information security analysts protect organizations from data breaches and hacks. They develop, implement, and enforce security measures to protect sensitive information by performing risk assessments, installing and implementing security controls, and doing defense planning to prevent future security incidents.
- Average Salary
Information security analysts received a median salary of $102,600 ($49.33/hour) in 2021, according to the U.S. Bureau of Labor Statistics.
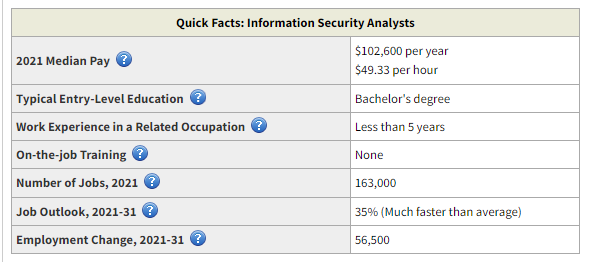
Source: US Bureau of Labor Statistics
- Skills Needed
Information security analysts must have knowledge of computer security basics, including firewalls, routers, and other security infrastructure. Knowledge of penetration testing and network protocols is advantageous. They must also have good communication skills to communicate security policies and procedures to non-technical audiences.
Related Read: 13 Best Information Security Courses
Incident Response Analyst
- What They Do
Incident response analysts work with an incident response team to intervene in cyberattacks. Their job is to reconstruct the events of the breach using forensic analysis and determine the intruder’s entry point, if any damage was caused, and identify if the intruder is still present. Incident response analysts follow procedures outlined in the organization’s Cyber Security Incident Response Plan (CSIRP).
- Average Salary
According to ZipRecruiter, the average salary for an incident response analyst is $104,664 per year ($50/hour).

Source: ZipRecruiter
- Skills Needed
As the “firefighters” of the security world, information security analysts need a degree in computer science or general security certification such as the CompTIA Security+ certification offered by Springboard’s Cybersecurity Bootcamp. Incident response-specific certifications are also available, such as the SANS Institute’s Global Information Assurance Certification (GIAC) Certified Incident Handler (GCIH) or EC-Council’s EC-Council Certified Incident Handler (ECIH).
Risk Analyst
- What They Do
Cyber risk analysts are responsible for predicting the nature and scope of future cyber threats by researching the threat landscape to identify current trends. They also develop plans to prevent future incidents from occurring. Their responsibilities range from monitoring network activity for unusual activity to developing security awareness training programs and investigating security breaches.
- Average Salary
Cyber risk analysts earn an average salary of $92,802 per year, according to Indeed.

Source: Indeed
- Skills Needed
This is not an entry-level job. Professionals must demonstrate proven knowledge of network management, incident response, and DevOps. They must be able to architect, engineer, and implement security solutions in complex environments, and use monitoring, detection, and incident response to support ongoing security operations.
Penetration Tester/Ethical Hacker
- What They Do
Penetration testers simulate a cyber attack against an organization’s networks, systems, and applications to test the overall resiliency of its IT infrastructure. They use a variety of hacking tools and techniques to find vulnerabilities hackers might exploit. They run tests on applications, network devices, and cloud infrastructure, and write technical reports to communicate their findings.
- Average Salary
Ethical hackers earn an average base salary of $104,454, according to Salary.com.
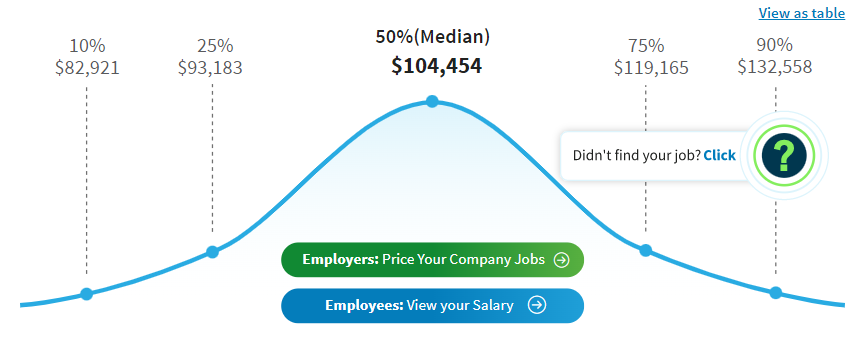
- Skills Needed
Knowledge of specific computer languages such as Python, Powershell, Golang, and Bash is essential, plus experience with pentest management platforms such as Wireshark, Kali Linux, and Nmap. They also need to be fluent in threat modeling, cryptography, cloud architecture, remote access technologies, and technical writing/documentation.
Security Engineer
- What They Do
Security engineers design, implement and monitor security controls to render computer systems resistant to malware attacks and natural disasters. They plan computer and network upgrades, troubleshoot issues, and respond to security incidents. They also perform security assessments and code audits.
- Average Salary
The average salary for a security engineer is $75,376/year, according to Indeed.com.

Source: Indeed
- Skills Needed
Security engineers must know programming languages, including C++, Python, PHP/Hack, Golang, and Java, and have experience designing and implementing back-end security-enhancing features. Mastery of at least one of the following areas is essential: authentication, authorization, applied cryptography, key management systems, and public key infrastructure.
Getting Into Cybersecurity
There are many ways to get into cybersecurity, from pursuing a four-year degree to enrolling in a bootcamp or pursuing industry certifications. Let’s break down what some of those paths look like:
What Skills Do You Need?
Cybersecurity is a challenging field that requires knowledge of several programming languages, problem-solving abilities, and familiarity with industry-standard tools and platforms.
Related Read: 20 Cybersecurity Skills to Boost (or Jumpstart) Your Career
Technical Skills (Programming Languages, Network Administration, Operating Systems, Risk Analysis)
To work in cybersecurity, you’ll need to know Python, Shell scripting, HTML, Javascript, and SQL. You should also be familiar with the network administration (procedures for managing, monitoring, and maintaining an organization’s networks using network monitoring and security controls).
Soft Skills (Problem-Solving, Critical Thinking, Teamwork, Flexibility)
Cybersecurity professionals need problem-solving skills to gather business requirements and craft the right solutions. Verbal and written communication skills are paramount as you’ll work closely with clients, propose solutions, and educate non-technical employees on security policies and procedures.
Background To Enter This Field
Degree
A four-year degree in IT or computer science shows prospective employers you have the skills needed for the job. Some universities offer degree programs in cybersecurity engineering or cybersecurity operations. Other popular degrees for a career in cybersecurity include database management, computer hardware engineering, network administration, computer forensics, and machine learning.
Bootcamp
Bootcamps are intense programs lasting a few weeks to a few months, and are designed to prepare students for entry-level jobs. Graduates typically emerge with a certificate and professional portfolio. Springboard’s Cyber Security bootcamp is a 6-month program that prepares students to take the CompTIA Security+ exam and earn a recognized industry certification.
Certification
Many companies prefer candidates who have certifications to validate knowledge of best practices. Some job listings require specific certifications such as CISSP, CISA, CISM, Security+, CEH, and more. Some certifications are vendor-specific, while others are domain-specific.
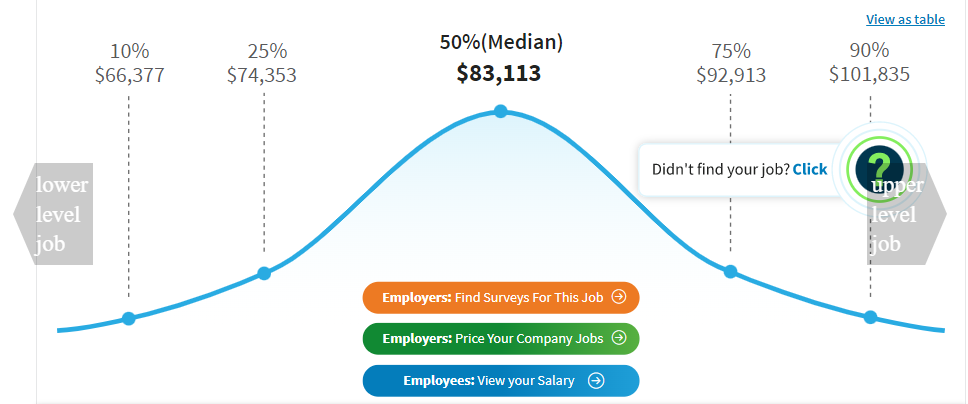
Average Salary
Here’s the average salary of a cybersecurity specialist:
Entry-Level
The average salary for an entry-level cybersecurity professional is $73,242, according to Salary.com.

Mid-Level
The average salary for a mid-level cybersecurity professional is $83,113, according to Salary.com.
Senior-Level
The average salary for a senior-level cybersecurity professional is $140,007, according to Salary.com
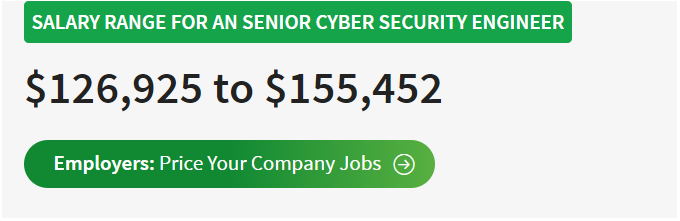
Source: Salary.com
FAQs About Cybersecurity
We’ve got the answers to your most frequently asked questions:
Is Cybersecurity a Good Career?
Cybersecurity is a good career choice for professionals who want a high starting salary and opportunities for advancement. The US Bureau of Labor Statistics predicts that employment for information security analysts will grow 33% from 2020-2030, much faster than the average growth rate for all occupations.
The shortage of cybersecurity professionals gives job seekers more bargaining power. According to Cybersecurity Ventures, the number of unfilled cybersecurity jobs worldwide grew by 350% from 2013 to 2021. The study predicts that the same number of jobs will remain unfilled by 2025.
Related Read: Cybersecurity Career 101: How to Start from Scratch
Do All Companies Need Cybersecurity?
Yes. All companies, from large enterprises to startups, are vulnerable to cyberattacks and therefore need to use cybersecurity controls to mitigate potential risks and prevent attacks.
What Is the Difference Between Cybersecurity and IT Security?
Cybersecurity is a subcategory of IT security. IT security focuses on protecting the hardware and software systems that store and transmit data, while cybersecurity focuses more narrowly on protecting computer systems and digital devices.
Since you’re here…
Interested in a career in cybersecurity? With or Cybersecurity Bootcamp, you’ll get a job in the industry, or we’ll return your tuition money. Test your skills with our free cybersecurity course, and check out our student reviews. We’re a safe bet. 🔒😉







